Cambium Data Blog
Nowadays, “the office” is digital, accessed from one’s home, adding an extra layer to the responsibilities of the human resources professional. After all, slow connections, login issues, and other problems can and do exacerbate burnout, leading to turnover.
Let’s take a moment to consider how technology can help the modern HR department in its daily operations.
Let’s say you implement new software for your team to use, and they simply don’t.
Despite what you may assume, it likely isn’t because they’re being lazy or assembling in an act of quiet defiance. They may just be burnt out.
It is becoming increasingly difficult to get excited about new technologies, especially in the workplace. For your team members, it amounts to just another thing they have to juggle.
Communication is a critical element of any business’ success, but perhaps more so in the average small or even medium-sized organization. Internal communications can make or break profitability, especially if they fail. Disconnected files and ongoing email chains often translate to duplicated efforts and missed deadlines or opportunities.
Let’s talk about how you can avoid the kind of friction that hinders your ability to collaborate and holds back your potential for success.
Nowadays, businesses of all sizes rely so, so much on data. This makes it a hugely valuable asset. Unfortunately, it is also one of the most vulnerable.
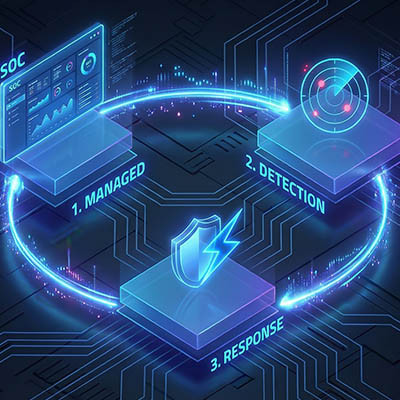
We’ve reached a point where the cybersecurity protections most have relied on for years—things like basic antivirus and its ilk—just aren’t enough to properly protect against modern attacks and their ramifications. To really protect your business, you need protections like Managed Detection and Response.
These days, it feels like every week there’s a new AI tool out there that promises to exponentially improve your productivity. It’s easy for leadership teams to fall victim to the “shiny object syndrome,” where they adopt a new tool only to find it’s not seeing any use after six months. New technology should never be a solution looking for a problem—instead, it should be a precision tool to fix a specific friction point in your business.
Negotiating an IT contract is often the most overlooked step in an SMB's technology journey. Many owners focus strictly on the monthly price, inadvertently leaving their business exposed to hidden fees, slow response times, and "vendor lock-in." To build a sustainable partnership, your contract must be a balanced document that rewards proactive management and provides clear accountability for your bottom line.
Connecting to a public network is a gamble with your data. Most people see free guest Wi-Fi as a convenience, but from a technical standpoint, it is a way for others to monitor your traffic. When you use these networks, you are trusting a third party to secure a connection that is often left intentionally wide open.
Imagine if a master locksmith suddenly announced that the standard deadbolt—the exact one installed on almost every office door in the country—had a hidden flaw. Worse, imagine they just proved exactly how to pick it. You wouldn't just sit there and hope for the best. You'd be calling a professional to get new, secure locks installed immediately.
I’ve spent my entire career telling people that technology is a tool to help you do more. Unfortunately, the bad guys have been using that same tool to build something truly unsettling: the deepfake.
We’ve officially entered an era where you can't necessarily trust your eyes or ears during a business call. It isn’t just for making funny movie parodies anymore; it’s being weaponized to bypass your security and drain your bank accounts.
Your most productive employees—the ones who consistently meet their goals and maintain the highest standards—are often the first to leave when a workplace fails to address recurring technical issues. You might not notice the shift immediately because these individuals typically continue to perform their duties without causing visible disruption.
Imagine getting to the office Tuesday morning, ready for another productive day, when your lead admin walks in with bad news. The file infrastructure is down, and so is everything else. It’s been encrypted by ransomware, and you’re the latest target of a zero-day ransomware attack that managed to bypass your antivirus. What do you do?
Most business owners I meet have a backup plan. In the worst situation, it's a lone external drive humming in the corner or a basic cloud sync. While these are good first steps, they often harbor a hidden danger: a single point of failure. If your office faces a fire, that external drive is toast. If a staff member accidentally wipes a folder and it instantly syncs to the cloud, your data could vanish before you even realize it's gone. To build a strategy you can actually sleep on, we use the 3-2-1-1 Rule.
Let me ask you something:
Do you think all the different tools, programs, and applications whose icons litter your business' desktops help drive your business forward? Or, is there a possibility that they are actually undercutting your team’s productivity?
The trouble with all these inclusive platforms is that they include more than you might realize… and as such, you’re likely investing in duplicate functionality. This is why it is so important to be able to say no, or to have someone in your corner who can.
The bigger your business’ workforce, the bigger your overall digital footprint… and the bigger a task it becomes to properly manage who has access to what. Make no mistake, this task is a critical one to complete for the sake of your security and, ultimately, your reputation and success.
Let’s go over how this situation arises and discuss how to avoid it through identity governance.
The workplace is a strange beast. You’re taking a group of people with wildly different personalities, throwing them together for 40+ hours a week, and asking them to act like a cohesive unit. It’s a mix of professional deadlines and how about those Mets? water-cooler talk.
Whether your office is a suite downtown or a series of icons on a taskbar, that blend of personal and professional is healthy. We’re social creatures, after all… but when those two worlds bleed into each other without any rules, things get messy—and I’m not just talking about hurt feelings. I’m talking about security risks that could cost you $15,000 (or much, much more).
Can you say with absolute certainty that your business could survive a total server failure tomorrow morning? If the answer is no, then you have work to do getting your data backup systems into a better place. Most small businesses believe that having a backup running is the same as their data being safe, but that’s simply untrue. Having a backup is half the battle; making sure the backup works is another story.
Typically, when we make a mistake in a word processor, we just hold down the Backspace key until you get rid of the error, but when you consider all the times you have to hold down the key for longer than five seconds, that time adds up. To bypass this inefficiency entirely, you can use a little tool called “Fast Delete.” Here’s how it’s done.
On March 23, 2026 the Federal Communications Commission (FCC) expanded their banned list of hardware to include all consumer-grade Wi-Fi routers produced outside the United States. This designation identifies such equipment as a threat to national security. Under this new regulatory framework, the import, sale, and use of most existing router models are prohibited because a device is classified as foreign-made if any significant portion of its design, component manufacturing, or assembly occurs outside of domestic borders.